You can now import X.509 certificates in your Trusted Entities signed with the following key types:
- EC: P-256, P-384, P-521 and secp256k1
- OKP: Ed25519, X25519
- RSA
See the most recent changes in Paradym.
April 28, 2026
You can now import X.509 certificates in your Trusted Entities signed with the following key types:
April 22, 2026
We've added two new webhook events, that can serve as an additional way to handle certain alerts that would otherwise be sent by e-mail in an automated fashion:
certificate.renewal.required for when a certificate is due for renewal.trustedEntity.etsiLote.update.failed for when an ETSI LoTE update has failed.April 8, 2026

We've added activity analytics to the overview page, giving you better insight into how your project is performing.
These analytics help you quickly understand usage patterns, monitor performance, and identify potential issues at a glance.
April 2, 2026
Fixed an issue where removing a CSR would remove the associated signing key, even if the CSR already reached the imported status. It now only removes associated signing key if the CSR has not reached the imported status yet.
April 1, 2026
With this release, we are adding experimental support for ETSI Lists of Trusted Entities (LoTEs).
A LoTE is a digitally signed list of trusted entities, published as part of the European Digital Identity (EUDI) trust framework. Instead of manually adding individual X.509 certificates for each trusted entity, you can point to a LoTE URL and Paradym will automatically fetch the list, verify its signature, and extract the certificates it contains. Read more about how this feature works on our documentation.
This feature is based on standards that are still in development and is therefore experimental. It is subject to change, so please use it with caution.
March 26, 2026
Fixed an issue where you could link Trusted Issuers from a different project to a Presentation Template using the API.
There have been no cross-project usages.
March 13, 2026
OpenID4VC Verification sessions now have a new requestRetrieved state, allowing you to react to the user having retrieved the verification request.
This can be useful if you want to hide the deeplink or QR after is has been clicked/scanned, to prevent the user from scanning it multiple times.
The new state value can be subscribed to through webhooks using the new openid4vc.verification.requestRetrieved event. You can read more in the webhooks documentation. If you want to use the new event but only subscribe to specific events for your webhooks, you should update the webhook to also listen to the new request retrieved event.
March 10, 2026
You can now import X.509 certificates where the hash algorithm uses a different length than the key size. This means you can import an X.509 certificate with a P-256 that is signed using ECDSA with SHA-384 or SHA-512 hashing algorithms. ECDSA certificates signed by Paradym will still always use ECDSA with SHA-256 when using the P-256 key type.
March 9, 2026
With this release, we are expanding the OpenID4VC Issuance capabilities when using an Attribute Provider. The Attribute Provider can now defer the issuance of a credential, in case it is not ready yet. For more information, please check the Attribute Providers documentation.
March 5, 2026
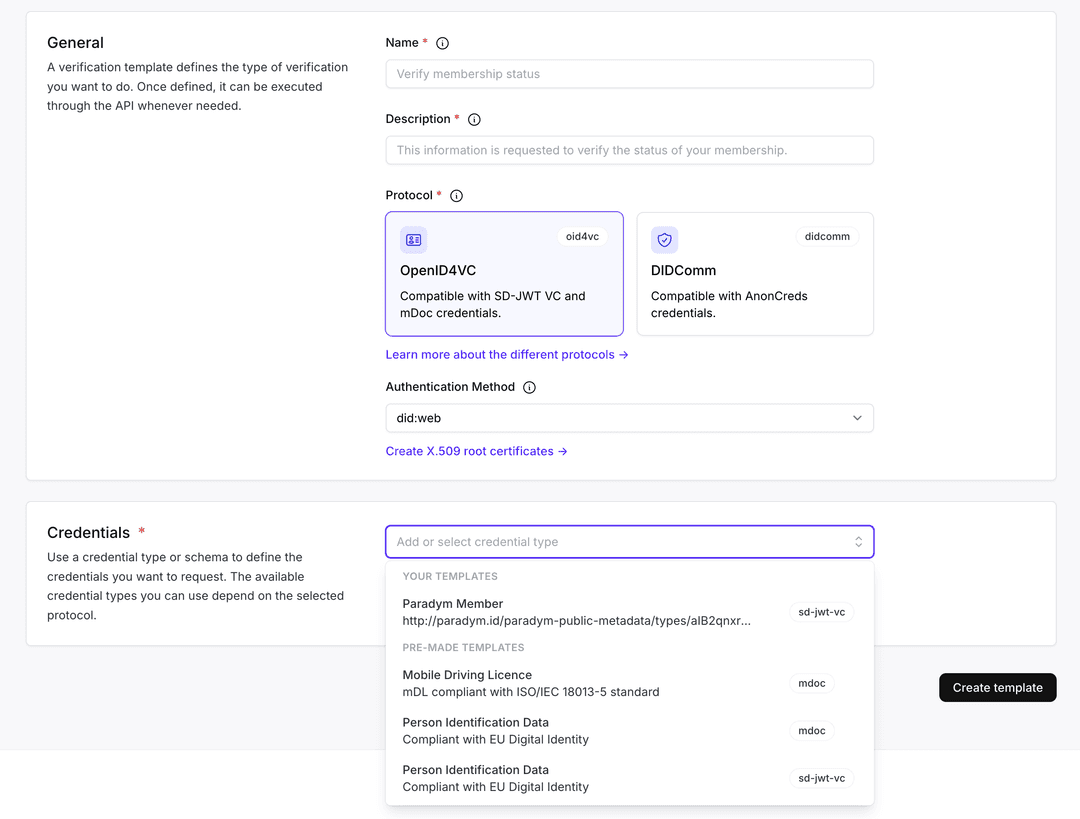
To make getting started with verifications easier, we've added pre-made presentation templates for verifying Person Identification Data (PID) and Mobile Driving Licences (mDL).
You can select these templates directly from the dashboard when creating a presentation template, and adjust the requested attributes to fit your use case.